For several years now, security experts have been worried about an event that could wreak havoc in the global economy.
This event threatens the security that protects much of our private information: from our private messages on WhatsApp to our bank details and phone calls.
In security circles its known as the “Z date”.
On this date, a new system of computing will emerge that will be able to crack traditional methods of encryption.
And suddenly all gates will be open: any information that we send over in the internet will be left open to hackers, spies, governments and criminals.
According to research by Michele Mosca, co-founder of the Institute for Quantum Computing, this danger point is fast approaching.
In 2016, he estimated that the Z date has a 15% chance of arriving before 2026.
But leaked research paper this month from Google suggests that the date could come sooner that we thought.
It could come within five years.
And it’s causing quite a serious amount of panic among governments and industry.
As the World Economic Forum put in their Global Risk Report for 2019…
“A collapse of cryptography would take with it much of the scaffolding of digital life.
These technologies are at the root of online authentication, trust and even personal identity.
They keep secrets—from sensitive personal information to confidential corporate and state data—safe. And they keep fundamental services running, from email communication to banking and commerce.
If all this breaks down, the disruption and the cost could be massive.”
Losing the Keys to Digital Life
What is causing this problem?
It’s all down to the way we encrypt information.
Let me explain. The goal of encryption is to garble data in such a way so that no one who has the data can read it unless they are the intended recipient.
And the way we do that is to make use of a very specific maths problem.
And it’s this…
As far as we can tell, it’s very difficult to take a really big number and find it’s factors: the two numbers that multiplied together will give you that large number.
We can multiply two numbers together. That’s easy.
But doing the reverse: finding the factors that multiply together to get a large number is actually extremely hard.
Take this large number.
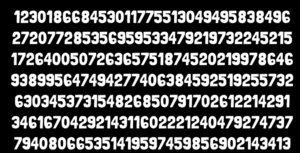
It took 2,000 years of computing processor time to find the prime numbers that multiply together to get this long number.
And this is very useful for encryption…
Because if you have access to the two factors, then you can use them to access private information.
But if you don’t have the factors, then the data is effectively encrypted.
The Quantum Nightmare
And that all works well and good as long as we are talking about normal computers.
The problem is that what is considered safe encryption today will soon be undermined by quantum computing.
Quantum computers are actually very good at taking random numbers and then generating very good estimates of the factors.
It has been estimated that it would take quantum power of 4,000 qubits to break today’s ”strong” encryption keys.
Estimates suggest we may see this capability by 2023.
However, weaker encryption algorithms will be threatened sooner, and the clock is clearly ticking on all of today’s methods.
“Anyone that wants to make sure that their data is protected for longer than 10 years should move to alternate forms of encryption now,” said Arvind Krishna, director of IBM Research.
Governments and industries are not waiting.
The European Telecommunications Standards Institute has even prepared a list of critical infrastructure targets:
- Government and military communications
- Financial and banking transactions
- Confidentiality of medical data and healthcare records
- Storage of personal data in the cloud
- Access to confidential corporate networks
All of these will be vulnerable, they say.
So yes: this is a very scary problem.
The good news is that quantum-safe encryption algorithms are already being developed by companies including Google and Microsoft to solve the issue.
According to the World Economic Forum…
“As the prospect of quantum code-breaking looms closer, a transition to new alternatives— such as lattice-based and hash based cryptography—will gather pace.
Some may even revert to low-tech solutions, taking sensitive information offline and relying on in-person exchanges.”
But they are still in the theoretical and testing stages.
The main challenge is retrofitting these new approaches into existing systems.
Quantum Computers: The Ultimate Weapon?
In fact, it is not just Google And Microsoft that are working on quantum cryptography.
The Pentagon…the Russians…the Chinese…governments will work away on developing this technology.
This is partly to protect their own banking and communication systems. But also because they recognise a weapon when they see one.
Just picture how much damage you could do with a computer that could crack encryption systems.
The panic you could create by removing the systems that protect state secrets, big banking transactions and the medical information of political leaders.
“We see this as a very disruptive technology,” said Michael Hayduk, chief of the computing at the Air Force Research Laboratory.
One risk is knocking out satellites…
“Highly secure encryption for communications satellites and accurate navigation that does not require GPS signals are some of the most coveted capabilities that would be aided by quantum computing.
The Pentagon is especially intrigued by the potential of quantum computing to develop secure communications and inertial navigation in GPS denied and contested environments.”
China is “very serious” about this, he said. It is projected to invest from $10 billion to $15 billion over the next five years on quantum computing.
China already has developed quantum satellites that cannot be hacked.
In fact, there is a whole field of “quantum stealth” technologies emerging.
And some of it is very weird.
Take Canada’s Hyperstealth Biotechnology.
This company manufactures camouflage uniforms for militaries across the globe.
Recently company patented a new “Quantum Stealth” material that disguises a military’s soldiers by making anything behind it seem invisible.
The material is paper-thin and inexpensive.
Step behind it and you disappear.
Just try spot the scientist in the still below.

Do you see him?
According to a press release, the technology works by bending the light around a target to make it seemingly disappear.
This light can be in the visible spectrum, or it can be ultraviolet, infrared, or shortwave infrared light, making the material what Hyperstealth calls a “broadband invisibility cloak.”
Hyperstealth say they are developing the material for use with tanks, aircraft and ships.
You can watch an hour of demonstrations here
A $50 billion market by 2030
For investors there should be plenty of interest in this field as well.
I’ve looked at D-Wave Systems before. They have developed a quantum computer that uses a method called annealing to become the first commercial quantum company.
We’ve also looked at the likes of Google are looking to develop quantum computers.
A quantum approach will be enable Google to perform tasks at speeds at least 400 times faster than that possible with conventional techniques.
They could accelerate their ambitions in artificial intelligence to scientific discovery.
The quantum computing market itself could be worth up to $50bn by 2030, according to Boston Consulting.
I’ll point to the risks and opportunities here in Monkey Darts.